Cybersecurity is no longer the sole domain of the CISO. For 2026 and beyond, cybersecurity must be positioned as a business decision with intentional alignment between CIOs and CISOs.
This was the central thesis of The CIO Cybersecurity Playbook for 2026 at this year’s Gartner IT Symposium/Xpo, where findings of its latest CIO/CISO partnership survey outline a comprehensive path for CIOs to align cybersecurity initiatives with business outcomes and expectations.
CIO vs. CISO
The CIO and CISO roles, though deeply intertwined, are not interchangeable. The CISO’s foremost objective is simple: “Don’t get hacked,” by balancing protection, cost, and operational enablement. The CIO, by contrast, must focus primarily on service delivery, IT cost management, and technology alignment with business priorities.
Yet this natural distinction can lead to misalignment.
Survey data reveals that 74% of CISOs who report to a CIO would prefer to report directly to the board or CEO, and a staggering 92% of those who already do want to keep it that way.
Meanwhile, only 35% of CIOs actually prefer that the CISO report to them. Notably, 41% of CIOs say the CISO should report directly to the board or CEO.
Still, CIOs must be aware of the trade-off. Conflict arises when CISOs operate outside the CIO’s reporting structure, particularly in areas such as technology debt, vulnerability management, and investment prioritization.
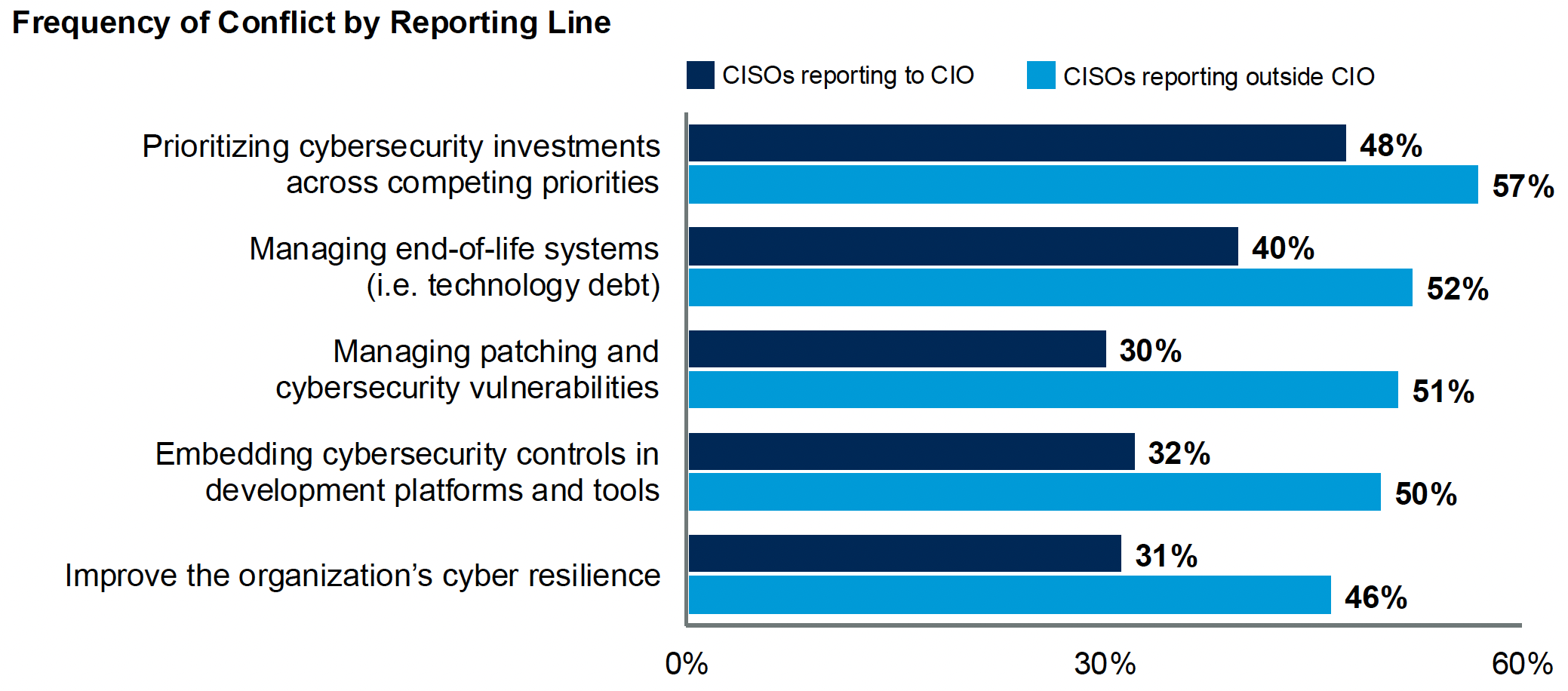
Source: Gartner (October 2025)
Build a Shared Governance Model
Governance is the CIO’s first pillar of cybersecurity leadership. To function effectively, the organization must align on:
- Accountability and decision rights
- What constitutes acceptable risk
- Risk-based controls and risk assessment
- Effectiveness assurance mechanisms
These conversations must be deliberate and codified.
A clear cybersecurity operating model enables consistency factors that influence execution at every level.
Metrics That Matter
CIOs increasingly face pressure to quantify cybersecurity performance. Traditional reporting focused on technical outputs like firewall logs or system uptimes often lacks relevance at the board level.
This is where Outcome-Driven Metrics (ODMs) come in, shifting the conversation from “what did we do?” to “what did we achieve?”
Key ODMs include, but are not limited to:
- Incident containment and remediation time
- OS Patching Cadence
- Percentage of Unassessed Third Parties
- Expired Policy Exceptions
- Security Awareness Training Outcomes
These metrics offer a simplified but powerful layer that helps CIOs explain cybersecurity performance to non-technical executives.
Crucially, they also support benchmarking, which allows organizations to compare protection levels against industry peers or risk appetite thresholds.
Reframing Cyber Risk as a Business Decision
Perhaps the most important message in the 2026 playbook is that cybersecurity is a business decision.
“Cyber risk is a business decision, its’s a choice, and most organizations don’t treat it like one.”
Paul Proctor, Distinguished VP Analyst, Gartner
It is impossible to eliminate all risk. Even with unlimited resources, perfect protection remains out of reach.
CIOs must help their organizations understand that cybersecurity is about making sustainable, defensible investments and not achieving impossible absolutes.
This is where Protection Level Agreements (PLAs) come into play.
Similar to service-level agreements, PLAs define a desired level of protection within a given budget.
For instance, an organization may decide that patching within 30 days is acceptable based on risk appetite and cost. The PLA formalizes that decision, creating a shared understanding across IT, security, and the executive team.
This approach enables a more productive question for the C-suite: “How much protection do you want, and how much money are you willing to spend to achieve?”
Connecting Cybersecurity to Enterprise Value
Beyond governance and metrics, CIOs must frame cybersecurity in terms of business outcomes. Cyber investment decisions must be prioritized not just based on their impact on operations, customer experience, and revenue.
To do this, CIOs can map security performance across business units.
For example, customer-facing platforms may require higher investment due to their direct influence on satisfaction and brand reputation, while back-office systems may tolerate slightly higher risk.
This business-value-centric model allows CIOs to:
- Identify underinvested, high-risk areas
- Allocate resources where they protect the most business value
- Show the board how cybersecurity supports revenue, compliance, and operational continuity
It also positions the CIO as a translator by connecting cybersecurity language to business strategy in a way that resonates with senior leadership.
Forward-Looking Leadership
The modern cybersecurity environment means CIOs must remain vigilant about emerging trends surrounding developing threats and regulatory requirements. Leaders must be able to anticipate risk and adapt proactively.
Regulatory compliance, in particular, must be managed without becoming the entire focus.
CIOs should ensure compliance boxes are checked, but never confuse them with holistic security. The real value comes from measurable outcomes and risk-informed decision-making.
During M&A due diligence, CIOs should incorporate ODMs as part of their integration assessments. Even if a target company can’t provide metrics, the absence of data itself can reveal maturity gaps, integration risks, or valuation concerns.
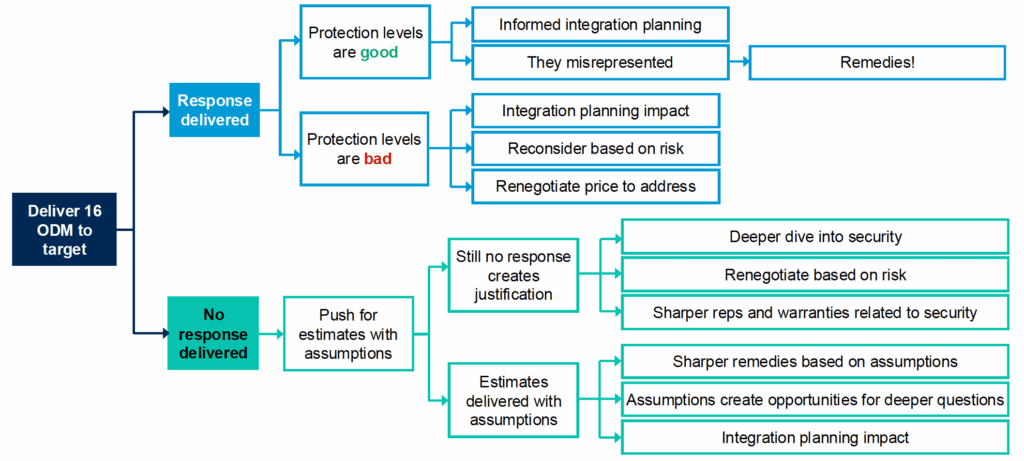
Source: Gartner (October 2025)
Using this lens, CIOs can more confidently assess cyber exposure and advocate for appropriate deal adjustments.
Trusted insights for technology leaders
Our readers are CIOs, CTOs, and senior IT executives who rely on The National CIO Review for smart, curated takes on the trends shaping the enterprise, from GenAI to cybersecurity and beyond.
Subscribe to our 4x a week newsletter to keep up with the insights that matter.
The Wrap
Gartner’s CIO Cybersecurity Playbook for 2026 shows that the CIO’s role in cybersecurity has never been more important. As technology is implemented deeper into the enterprise, the CIO must serve as a translator, strategist, and unifier.
To effectively achieve cybersecurity goals:
- Governance matters: Define roles, responsibilities, and decisions early.
- Metrics matter more: Outcome-driven metrics connect cyber investments to business outcomes.
- Risk is a choice: Protection Level agreements frame cybersecurity as a business decision.
- Culture counts: Elevate cyber awareness in IT and throughout the enterprise.
Cybersecurity is it’s an enterprise-wide responsibility. CIOs who lead with alignment and data will be best positioned to guide their organizations towards resilience in 2026.