Recent reports of a highly advanced United States F-35 stealth aircraft being successfully engaged over the skies of Iran have shocked some military analysts.
However, every smart military planner knows that there will one day be a countermeasure to your innovation. Even if you then implement a countermeasure to the original countermeasure, you will constantly have to remain alert to engineered solutions designed to defeat your innovation.
The same applies to the art and science of cybersecurity.
In April of 2025, the Cybersecurity and Infrastructure Security Agency (CISA) released guidance for government agencies and commercial entities concerning potential credentials compromise in the legacy Oracle Cloud. Hackers are increasingly bypassing perimeter defenses by stealing tokens, certificates, and API keys.
With its guidance, CISA is explicitly informing government agencies and commercial entities on how to ensure that stolen credentials cause the least damage to their organizations. However, what is implicitly stated is that credentials will eventually be exposed or compromised.
Military communications security (COMSEC) has addressed credential vulnerabilities by implementing a doctrinal concept known as cryptoperiod management. The underlying objective is to limit the operational value of any key that may be compromised. By routinely rotating keys, operational exposure can be significantly reduced.
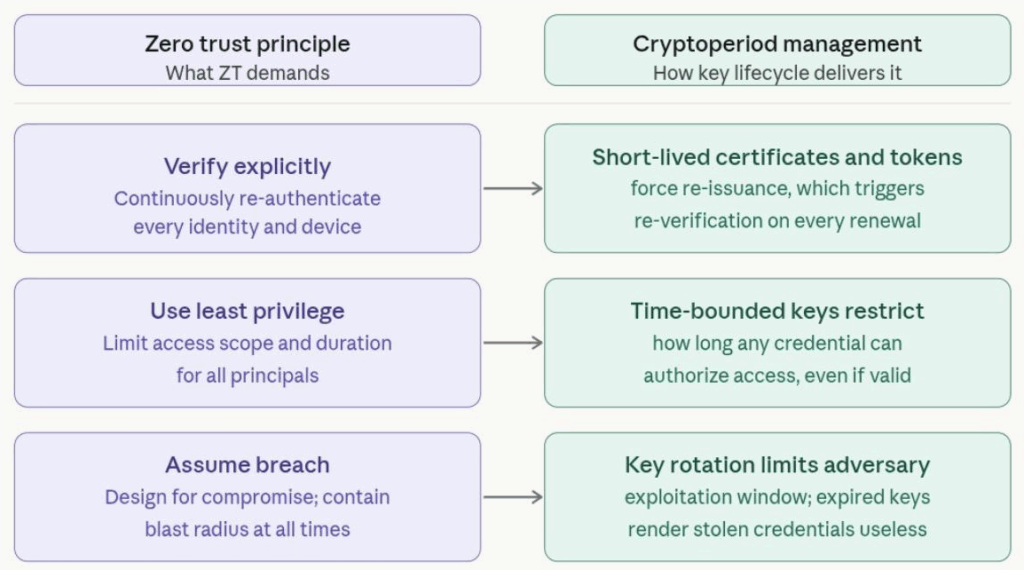
Interestingly, while the military has employed this technique for many decades, cryptoperiod management aligns closely with modern Zero Trust principles, as depicted in the chart below.
The espionage case of John Walker Jr., a U.S. Navy warrant officer, is widely regarded as one of the most damaging espionage incidents in the history of U.S. military communications security.
Walker, who began spying for the Soviet Union in 1967 and continued for nearly two decades, held positions that gave him control over physical cryptographic materials.
The Walker case fundamentally reshaped how the United States military approached cryptography, key management, and COMSEC. Many of the strict cryptographic discipline practices used today, particularly those related to key control and rotation, were reinforced or accelerated by lessons learned from the Walker espionage case.
From Military Origins to Commercial Application
One such innovation stemming from the Walker case was OverEmbracing Credentials Governance-the-Air Rekeying (OTAR). OTAR allows cryptographic keys to be replaced remotely and securely without requiring physical access to equipment.
Instead of manually loading new encryption keys onto a device, OTAR allows authorized personnel to securely push updated cryptographic keys over an existing communication network. The new keys are transmitted in an encrypted format to protect them during transit, and the receiving device automatically installs and activates them.
OTAR principles have significantly influenced and shaped modern credential and key management practices in the private sector, evolving far beyond its military origins into a foundational concept across several industries.
As an example, mobile device management relies heavily on over-the-air credential management.
SIM cards, embedded SIMs (eSIMs), and mobile applications receive cryptographic updates, security patches, and new authentication credentials pushed remotely by carriers and developers. This allows companies to address vulnerabilities and refresh security credentials across millions of devices simultaneously, without physical access.
Modern cloud platforms such as AWS, Microsoft Azure, and Google Cloud have adopted OTAR-inspired practices through automated key rotation services.
Rather than requiring administrators to manually update cryptographic keys across thousands of servers and endpoints, these platforms allow organizations to remotely rotate, revoke, and redistribute encryption keys across entire infrastructures with minimal human intervention, thus mirroring the core concept of OTAR.
Embracing Credentials Governance
Without clearly defined lifecycle controls, cryptographic trust can become a liability rather than an asset. Enterprises that fail to govern the full lifespan of their credentials and keys expose themselves to unforeseen risk.
While it is expected that cloud service providers and mobile device companies will implement strict credential controls, all industries reliant on IP information systems should hold themselves to the same high standards, given the evolving threat landscape (i.e, countermeasures).
There are multiple industry frameworks that establish credential management as a core security requirement.
NIST SP 800-53 provides the most granular guidance, governing how organizations authenticate users, enforce least privilege, and manage credential lifecycles.
On the cryptographic side, NIST SP 800-57 serves as the authoritative standard for key lifecycle management, defining how long a cryptographic key should remain in service based on the sensitivity of the data it protects, the strength of the underlying algorithm, and the volume of data encrypted under it.
Regardless of the framework consulted, business enterprises should establish and enforce credential and key lifecycle management practices that include the following:
- Defined Expiration Policies: Every credential, certificate, and cryptographic key should have a clearly defined validity period appropriate to its use case and risk profile.
- Automated Rotation: Manual key rotation is error-prone; enterprises should invest in automated platforms that rotate credentials on a scheduled or event-driven basis.
- Ownership Accountability: Every credential should have an assigned owner responsible for its renewal, rotation, or revocation.
- Continuous Inventory & Visibility: A centralized credential inventory that tracks issuance, expiration, and usage is foundational to lifecycle management.
- Revocation Workflows: Enterprises must have established, tested processes to rapidly revoke credentials.
- Audit & Compliance Reporting: Credential issuance, rotation, expiration, and revocation should be logged and auditable to support regulatory compliance.
The Wrap
The security practices now promoted under the banner of Zero Trust architecture are not entirely new concepts. Many of these principles have long been embedded in military communications security doctrine.
The military practice of controlling the cryptoperiod demonstrates that effective cybersecurity requires acknowledging the possibility of compromise and designing systems to limit its impact. Frequent key rotation, strict credential accountability, layered encryption architectures, and rapid revocation capabilities ensure that stolen credentials cannot be exploited indefinitely.
As organizations increasingly rely on cloud services and automated infrastructure, adopting these principles becomes essential.
By implementing disciplined credential lifecycles and enforcing regular key rotation, modern enterprises can replicate a security model that has protected military communications for decades.
Trusted insights for technology leaders
Our readers are CIOs, CTOs, and senior IT executives who rely on The National CIO Review for smart, curated takes on the trends shaping the enterprise, from GenAI to cybersecurity and beyond.
Subscribe to our 4x a week newsletter to keep up with the insights that matter.






