Cybersecurity researchers have uncovered a new wave of QR code phishing, or quishing, attacks that utilize advanced visual and structural obfuscation techniques to bypass detection. These attacks are being carried out through phishing-as-a-service (PhaaS) platforms like Gabagool and Tycoon, and are explicitly designed to compromise Microsoft user accounts.
Tactics involve novel methods such as splitting QR codes into multiple images, nesting malicious codes within legitimate-looking ones, altering QR colors, and even drawing codes directly in content streams to defeat traditional security scanning tools.
Experts are urging organizations to adopt multimodal AI defenses capable of visually analyzing and decoding QR code payloads to stay ahead of evolving threats.
Why It Matters: Organizations adopting QR codes for convenience and security means cybercriminals are adapting, turning the trust in QR authentication into a phishing vulnerability. These latest techniques evade standard detection systems and exploit branding and urgency tactics to deceive users into surrendering sensitive Microsoft credentials.
- Split QR Code Technique Bypasses Traditional Image-Based Security Tools: The Gabagool phishing kit is employing an innovative approach where a QR code is split into two separate image files and embedded in phishing emails. To automated security systems they appear as harmless, unrelated graphics. However, when rendered together in the recipient’s inbox, they form a fully functional QR code that can be scanned by the user’s mobile device. The code typically redirects to a fake Microsoft login page crafted to harvest usernames, passwords, and potentially even multi-factor authentication codes. This approach highlights how attackers are prioritizing evasion at the image processing level, exploiting limitations in current email security systems that are not equipped to reassemble and analyze QR fragments.
- QR Code Nesting Adds a Layer of Visual Obfuscation to Avoid Detection: Tycoon, another phishing-as-a-service platform, has introduced the technique of QR nesting, where malicious payloads are hidden within or around seemingly legitimate QR codes. In one case, the outer visible code directed to a malicious site, while the inner section led to a trusted destination like Google. This hybrid approach generates ambiguity for both users and scanning software, raising the likelihood that the QR code will pass visual inspections and automated URL analysis. The familiar visual presentation appears functional, which makes users more likely to scan the code without suspicion and inadvertently trigger credential theft or malware downloads.
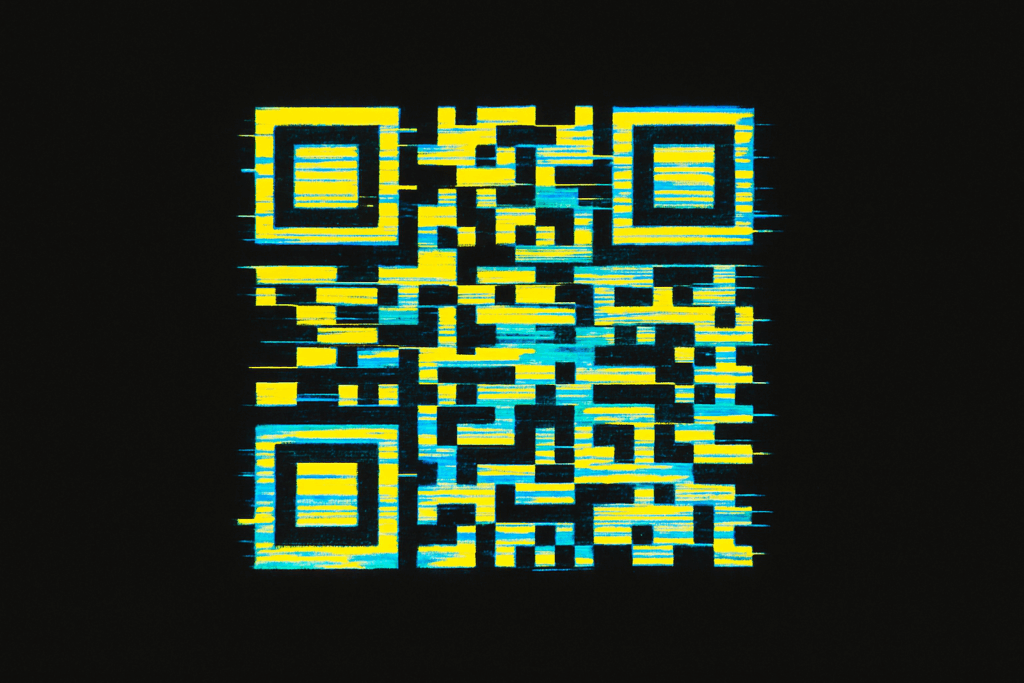
- Unconventional Color Schemes Confuse Optical Recognition Systems: Instead of the typical black-and-white design most QR readers and scanners are trained to recognize, attackers are now using non-standard color combinations that subvert detection. These modified visual formats can escape flagging by QR detection algorithms that depend on high-contrast edge detection to identify and decode patterns. Since many email gateways and endpoint security tools are optimized for traditional QR visuals, this tactic enables malicious code to sneak through initial defenses. Meanwhile, users may interpret these vibrant or stylized QR codes as part of a modern brand experience, further lowering their guard.
- Content-Stream Rendering Subverts Embedded Image Filters Entirely: The most technically advanced method observed in recent attacks involves drawing QR codes directly into a document’s content stream, rather than embedding them as typical image files. This allows attackers to avoid triggering image-based detection rules altogether, as the QR code is not stored as a JPEG or PNG but rather as vector-like instructions within the file. This technique is especially effective in PDF phishing emails and malicious attachments, where scanners are focused on embedded graphics. It highlights a significant gap within many email security tools, which may need to parse rendered content and static files to remain effective.
- Branding and Security Alert Impersonation Increases Credibility: Across Gabagool and Tycoon campaigns, attackers are heavily relying on brand impersonation to gain user trust. These phishing emails often mimic legitimate messages about security prompts or alerts. Creating a sense of urgency and referencing widely used platforms, emails encourage users to act quickly and scan the QR codes without pausing to verify the sender. This combination of technical sophistication and psychological manipulation makes the attacks particularly dangerous.
Go Deeper -> Weaponized QR Code Powers New Quishing Attack Targeting Microsoft Users – Cyber Press
Hackers Weaponize QR Codes in New ‘Quishing’ Attacks – Infosecurity Magazine
Trusted insights for technology leaders
Our readers are CIOs, CTOs, and senior IT executives who rely on The National CIO Review for smart, curated takes on the trends shaping the enterprise, from GenAI to cybersecurity and beyond.
Subscribe to our 4x a week newsletter to keep up with the insights that matter.