Although the United States and other countries and law enforcement agencies around the world have taken steps to cripple cybercriminals, it’s never been more crucial to secure your organizations against cyberattacks. Security Magazine reported that cyberattacks rose 22% in 2022, and there are no signs of slowing down. Technology leaders take care to build systems impenetrable to bad actors, but no system is perfect and there are many ways to ensure your organization’s data is protected.
“Most security and risk leaders now recognize that major disruption is only one crisis away. We can’t control it, but we can evolve our thinking, our philosophy, our program, and our architecture,” said Richard Addiscott, Senior Director Analyst at Gartner.
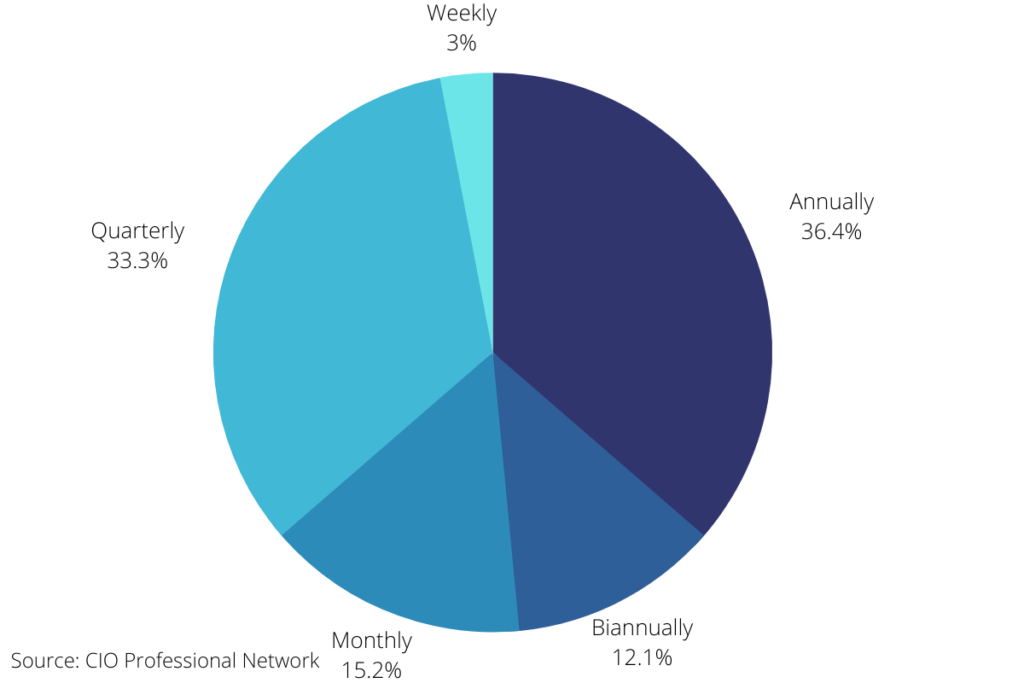
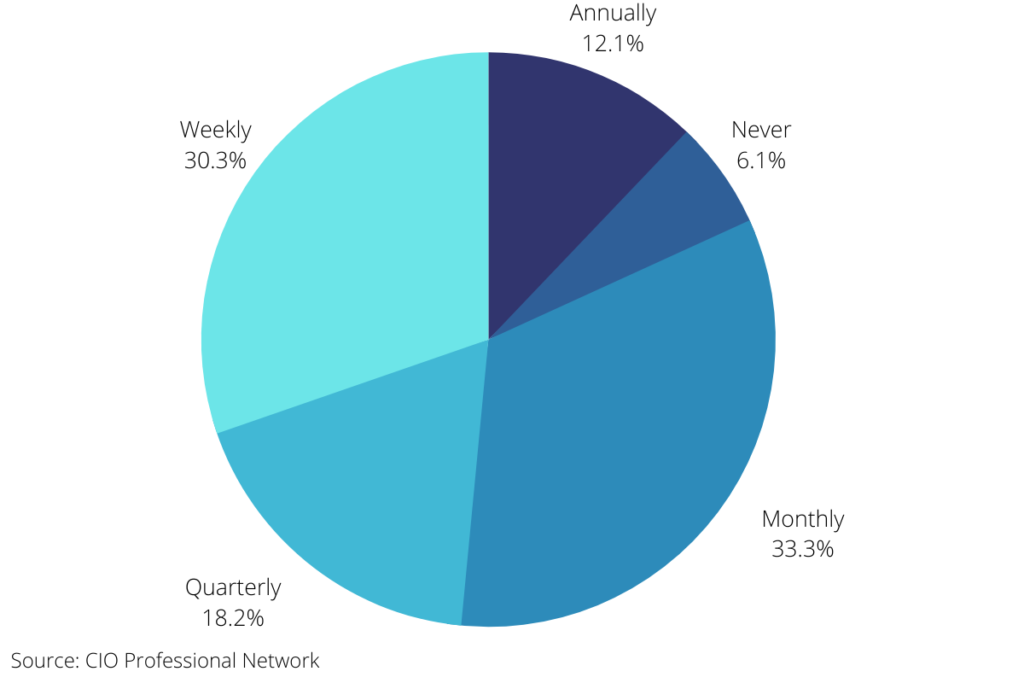
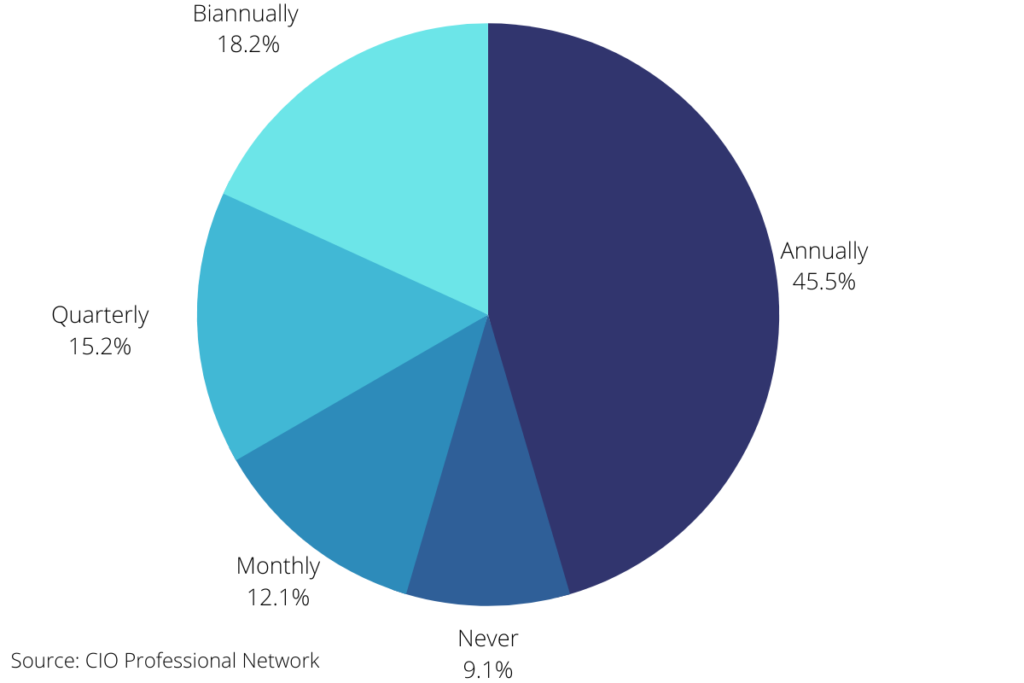
Members of the CIO Professional Network recently shared how often they test their cybersecurity measures for their organizations.
Penetration Testing
Penetration testing is a popular and effective method of sniffing out flaws by simulating an attack on a system. While pen testing cannot prevent bugs or flaws from going into production, it allows organizations to discover weaknesses that, on their own may not pose a threat but hackers may exploit as part of a broader attack.
A simulated attack will emulate how most threat actors would behave, allowing organizations to better plan for an attack.
Because penetration testing is often labor-intensive and costly, 80% of CIO Professional network members reported utilizing it only up to a few times a year. 36% of CIO Professional Network members participate in pen testing annually, 33% test quarterly, and 12% test biannually.
Phishing Simulations
Most attacks often begin with end-user failure that allows hackers to steal user data like login credentials to gain access to an organization’s systems. Phishing is a common social-engineering tool among cybercriminals because it is fairly easy to exploit human behavior to steal sensitive data. Organizations build phishing awareness into user security awareness because of the incredible damage to a company’s systems, revenue, and even reputation.
Educating end users is critical to organizational security, and 63% of members of the CIO Professional Network reported running frequent phishing simulations. 33% of members run phishing simulations monthly, and 30% test weekly. Surprisingly, 6% of members reported never running phishing simulations.
Tabletop Exercises
Since cyberattacks are the price of doing business in the digital age, as important as it is to prevent them, it is equally important to have a response plan in place. Tabletop exercises allow organizations to test their incident response plans and enhance and improve them.
Tabletop exercises can create opportunities for buy-ins by the business for future cybersecurity decisions and investments and highlight areas for improvement among teams and processes. 45% of CIO Professional Network members reported running tabletop exercises annually, 18% biannually, and 15% quarterly. 12% of members run tabletop exercises monthly, and 9% reported never running them.
Conclusion
Organizations cannot afford to take cybersecurity lightly. As cybercriminals become bolder and cyberattacks become more common, technology leaders are devising strategies to protect their organizations from all threats. As CIO Professional Network members have reported, there are many ways to ensure your organization is protected and that your processes are sound.






