CISOs and CIOs face a persistent challenge in translating cybersecurity risks into clear, compelling business language for their boards and executive teams.
To better understand which threats are hardest to explain at the leadership level, The National CIO Review conducted a community poll asking:
“Which risk is hardest to communicate to your board or executive team?”
The responses revealed a surprising result.
While every category drew significant concern, cloud misconfigurations and shadow IT emerged as the most difficult risk to convey, closely followed by several other threats, each with its own unique communication hurdle.
Cloud Misconfigurations and Shadow IT (21.0%)
Leading the poll with 21.0%, cloud misconfigurations and shadow IT topped the list as the most challenging risks to communicate to executives.
While enterprises accelerate digital initiatives and embrace multi-cloud ecosystems, security teams are often left reacting to issues caused by unsanctioned tools, misconfigured environments, or rushed deployments. These errors may be invisible to leadership until they result in a breach or audit failure.
Why its hard to explain:
- The risks are technical and often behind-the-scenes.
- Business units may see these issues as agility instead of a vulnerability.
- There’s often no “event” to showcase until a problem arises.
CIOs and CISOs are working to bridge this communication gap by tying these risks to tangible business outcomes, highlighting how a single overlooked setting can expose critical data or compromise compliance efforts.
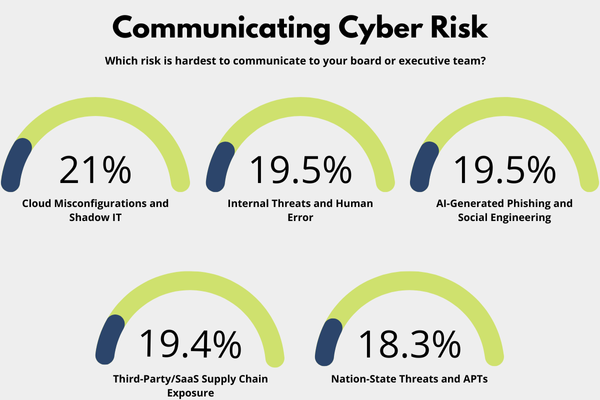
Internal Threats and Human Error (19.46%)
Tied for second, internal threats and human error accounted for 19.46% of responses. Accidental data leaks, shared credentials, and policy violations caused by employees are not easy to present to a board focused on growth and efficiency.
Communicating this type of risk can feel accusatory or personal, especially when the vulnerabilities stem from well-intentioned team members.
Why it’s hard to explain:
- It implicates internal behavior.
- Leaders may assume training alone solves the problem.
- These issues often lack clear, quantifiable metrics.
To overcome this, security leaders are repositioning the narrative to resilience. Emphasizing security culture and risk-aware behaviors helps boards view the issue as a structural opportunity for improvement, rather than a personnel problem.
AI-Generated Phishing and Social Engineering (19.46%)
Also taking 19.46% of votes, AI-enhanced phishing and social engineering represent a rising threat category that many executives struggle to visualize.
Thanks to generative AI, attackers can now craft more believable campaigns with alarming ease.
Why it’s hard to explain:
- The tactics are new, fast-evolving, and not widely understood.
- Real-world examples may seem like science fiction.
- Boards may see this as a continuation of “typical” phishing.
Security leaders are responding by showcasing simulations and threat models that illustrate the speed and realism of AI-generated attacks. Demonstrating how a convincing message can override even the most trained employee’s instincts is a powerful tool for executive awareness.
Third-Party/SaaS Supply Chain Exposure (19.37%)
At 19.37%, third-party and SaaS-related risk continues to gain attention as a serious communication challenge. With organizations increasingly relying on external platforms and cloud-based services, visibility into vendor vulnerabilities is often limited.
The complexity also lies in articulating the cascading impact a single vendor failure can trigger.
Why it’s hard to explain:
- The threat feels one step removed from core operations.
- Vendor trust can create a false sense of security.
- It’s difficult to show how small dependencies can lead to large-scale breaches.
CIOs and CISOs are increasingly turning to risk dashboards and relationship maps to visualize supply chain exposure, aligning third-party security discussions with business continuity and reputational concerns.
Nation-State Threats and APTs (18.34%)
Although ranked lowest, nation-state threats and APTs (Advanced Persistent Threats) still garnered a significant 18.34% of the vote.
These risks often involve high-stakes targets and complex attribution. Yet in many boardrooms, they remain misunderstood or seen as hypothetical, reserved for governments or critical infrastructure.
Why it’s hard to explain:
- The geopolitical layer adds abstraction.
- Attribution is often unclear or speculative.
- The threat feels distant from day-to-day business concerns.
To close this gap, security executives are focusing on impact instead of attribution. Boards need to know what’s at risk and what recovery could look like if an attack succeeds.
The Wrap
This poll paints a clear picture that no cyber risk is easy to communicate.
Each threat, regardless of origin, requires a different strategy for gaining executive alignment.
Boards need a clear understanding of risk in business terms:
- Which systems are vulnerable?
- What’s the cost of inaction?
- How will this impact operations, brand, or compliance?
Effective CIOs and CISOs are embracing narrative and practical demonstrations to translate threats into boardroom priorities.
Cybersecurity doesn’t speak for itself. Technology leaders need to develop a business-savvy voice at the table to be effective in their roles.
Trusted insights for technology leaders
Our readers are CIOs, CTOs, and senior IT executives who rely on The National CIO Review for smart, curated takes on the trends shaping the enterprise, from GenAI to cybersecurity and beyond.
Subscribe to our 4x a week newsletter to keep up with the insights that matter.